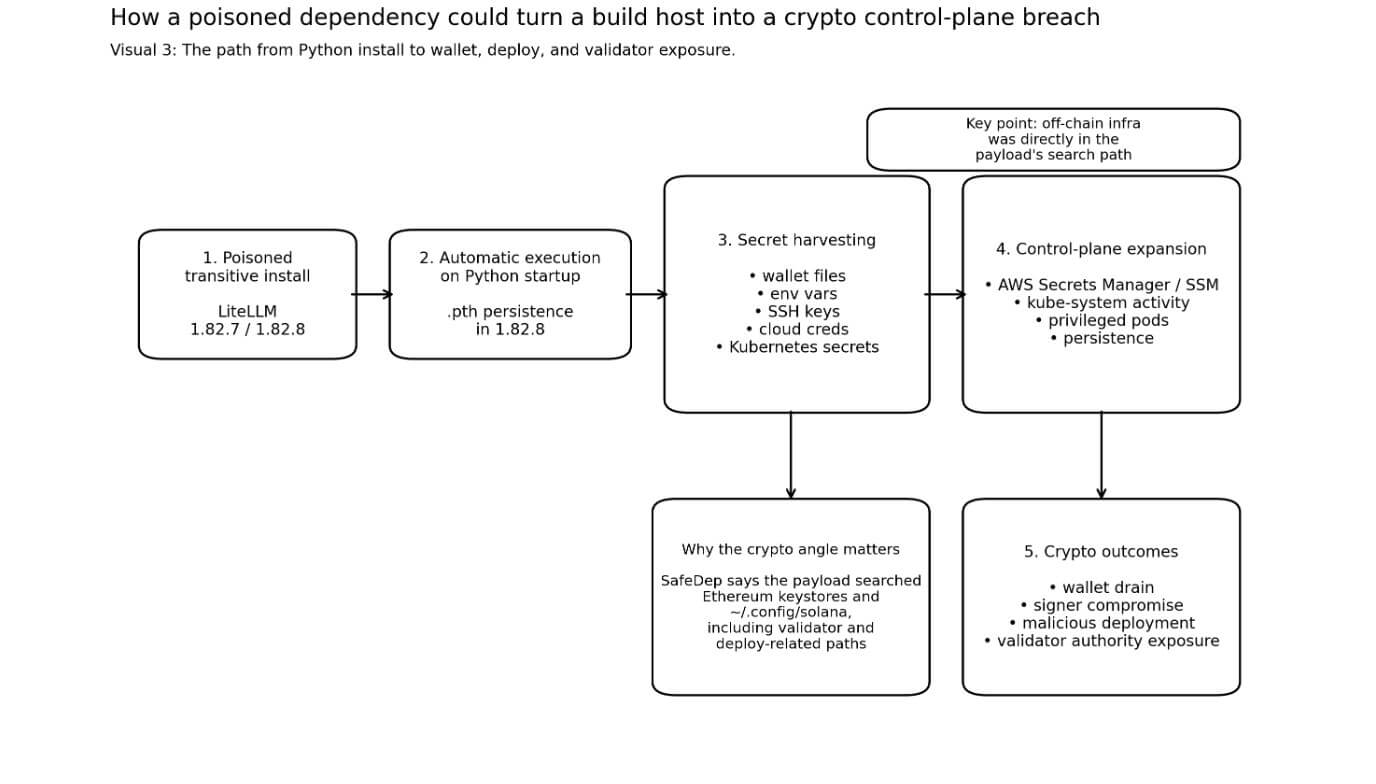
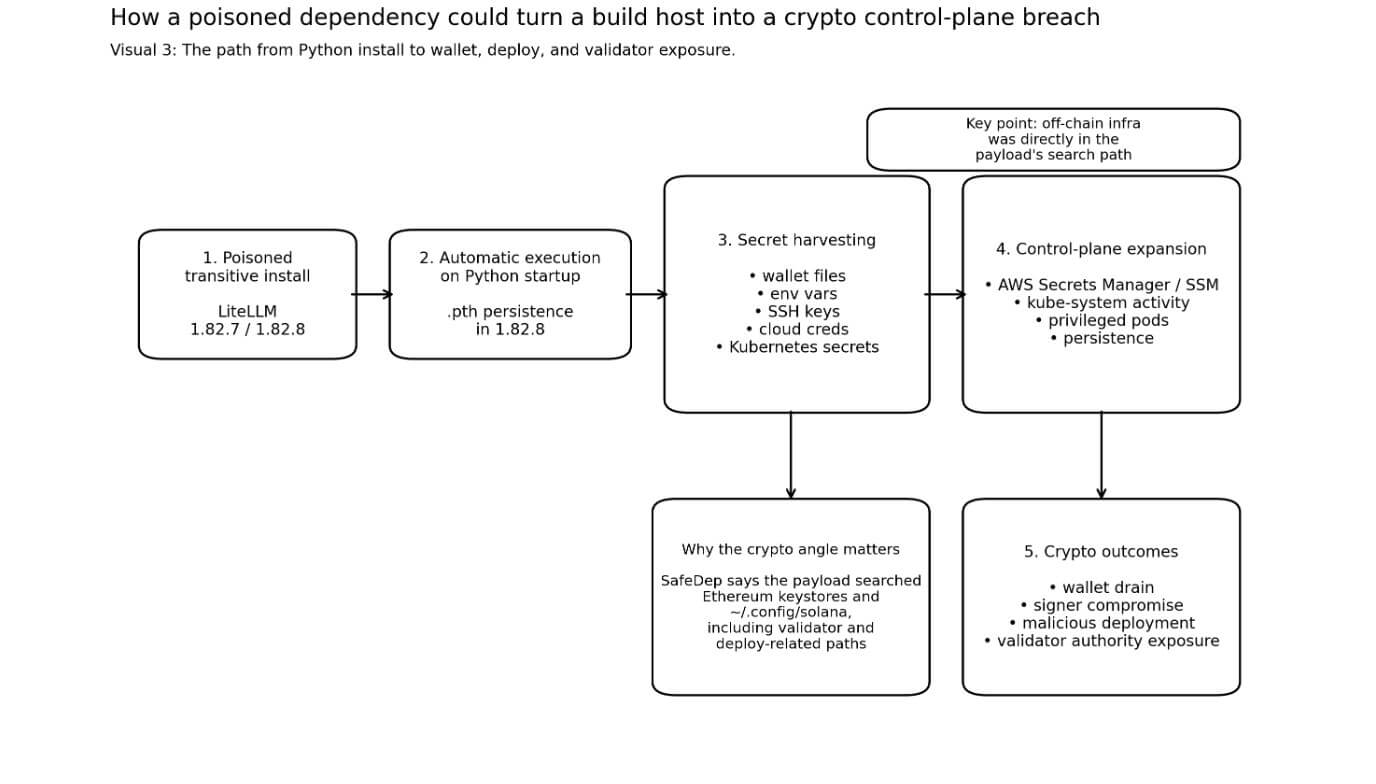
The poisoned launch of LiteLLM turned a routine Python set up right into a cryptographically conscious secret stealer that searches for wallets, Solana verification knowledge, and cloud credentials each time Python begins.
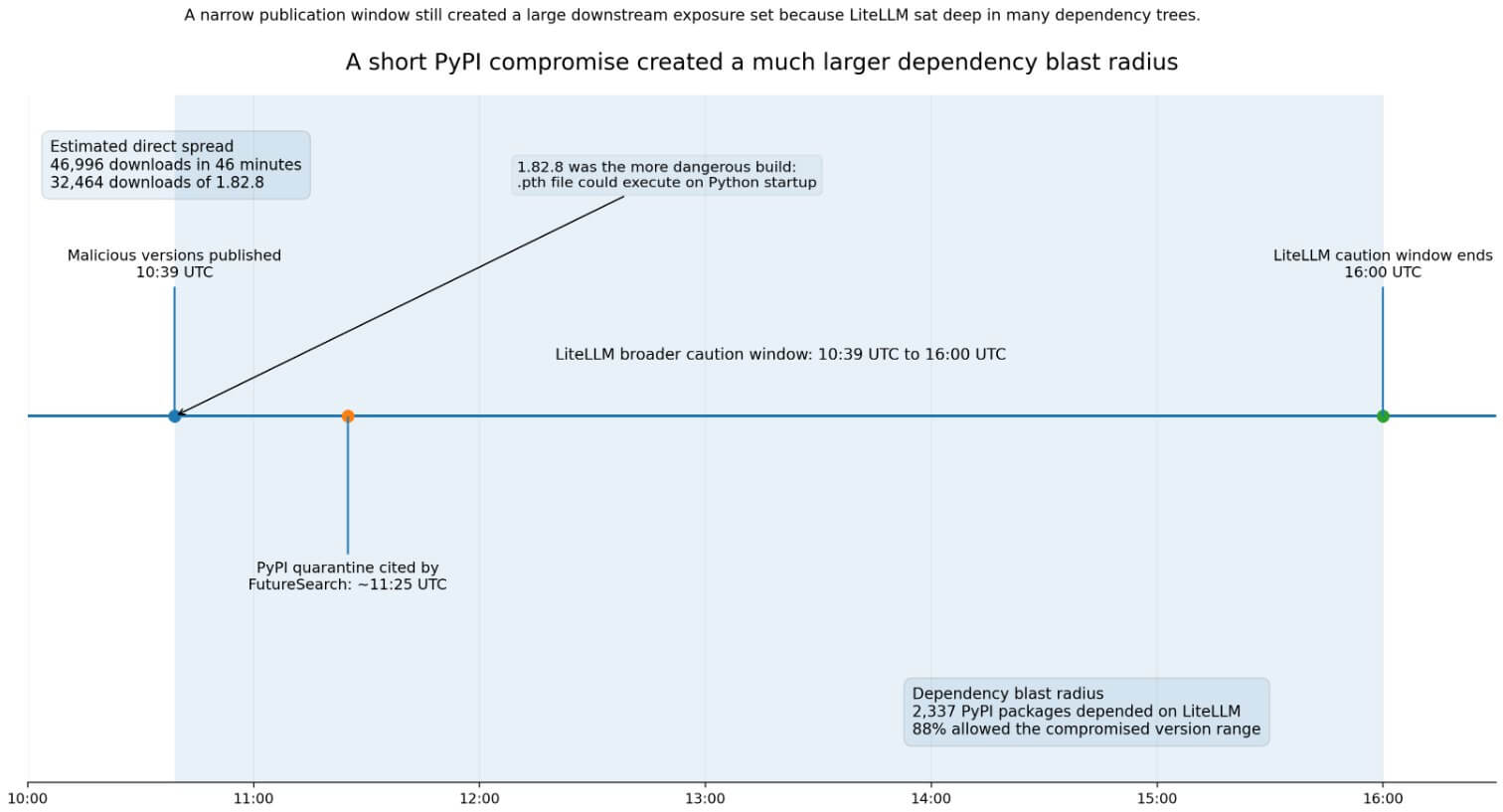
Between 10:39 UTC and 16:00 UTC on March twenty fourth, an attacker who gained entry to the maintainer account printed two malicious variations of LiteLLM (1.82.7 and 1.82.8) to PyPI.
LiteLLM markets itself as a unified interface to over 100 massive language mannequin suppliers, and by design sits inside a credential-rich developer setting. PyPI Stats has recorded 96,083,740 downloads within the final month alone.
The 2 builds had completely different ranges of danger. In model 1.82.7, you needed to import litellm.proxy on to activate the payload, however in model 1.82.8, a .pth file (litellm_init.pth) is embedded within the Python set up.
Python’s personal documentation confirms that 1.82.8 ran with none imports, as executable traces in .pth information are executed on each Python startup. The machine that had Python put in executed the compromised code the subsequent time Python was began.
FutureSearch estimates that 1.82.8 accounted for 32,464 of 46,996 downloads in 46 minutes.
Moreover, we counted 2,337 PyPI packages that trusted LiteLLM, with 88% permitting the model vary that was compromised on the time of the assault.
LiteLLM’s personal incident web page warns that anybody whose dependency tree incorporates LiteLLM by a transitive constraint that’s not pinned right into a window ought to deal with their setting as probably compromised.
The DSPy crew confirmed that LiteLLM is constrained to “1.64.0 or increased” and warned that contemporary installs throughout this era might resolve tainted builds.
Constructed to hunt cryptocurrencies
Reverse engineering of SafeDep’s payload reveals cryptocurrency targets.
The malware looked for Bitcoin pockets configuration and Pockets*.dat information underneath ~/.config/solana, Ethereum keystore directories, and Solana configuration information.
SafeDep stated the collector gave Solana particular remedy and confirmed focused searches of validator key pairs, voting account keys, and anchor deployment directories.
Solana’s developer documentation units the default CLI key pair path to ~/.config/solana/id.json. Anza’s validator documentation describes three permission information which can be central to validator operations, and states that theft of licensed drawers permits an attacker to achieve full management over validator operations and rewards.
Anza additionally warns that withdrawal keys ought to by no means be positioned on the validator machine itself.
SafeDep stated the payload collected SSH keys, setting variables, cloud credentials, and Kubernetes secrets and techniques throughout namespaces. As soon as we discovered legitimate AWS credentials, we queried AWS Secrets and techniques Supervisor and SSM Parameter Retailer for extra info.
I additionally created a privileged node-setup-*pod in kube-system and put in persistence by sysmon.py and systemd models.
For crypto groups, advanced dangers unfold in particular instructions. Infostealers that harvest pockets information together with passphrases, deployment secrets and techniques, CI tokens, or cluster credentials from the identical host can flip credential incidents into pockets exfiltration, malicious contract deployment, or signer compromise.
The malware assembled precisely that mixture of artifacts.
| Goal artifact | Path/file instance | why is it essential | Potential affect |
|---|---|---|---|
| bitcoin pockets file | pockets*.datpockets configuration file |
Pockets contents could also be uncovered | Threat of pockets theft |
| Ethereum key retailer | ~/.ethereum/keystore |
When mixed with different secrets and techniques, signer materials could also be uncovered | Signer Compromise/Deployment Exploitation |
| Solana CLI key pair | ~/.config/solana/id.json |
Default developer key path | Publicity of pockets or deployment privileges |
| Solana validator permissions file | Validator key pair, voting account key, licensed drawer | Central to validator operations and rewards | Violation of validator privileges |
| anchor deployment listing | Anchor-related deployment information | Deployment workflow secrets and techniques will be uncovered | Deployment of malicious contracts |
| SSH key | ~/.ssh/* |
Open entry to repositories, servers, and bastions | lateral motion |
| Cloud credentials | AWS/GCP/Azure setting or configuration | Prolong entry past localhost | Secret retailer entry/infrastructure takeover |
| Kubernetes secrets and techniques | Cluster-wide secret harvest | Open management aircraft and workloads | Namespace violation/lateral unfold |
LiteLLM’s incident notes hyperlink this breach to a earlier Trivy incident, and this assault is a part of a broader marketing campaign, as each Datadog and Snyk describe LiteLLM as a late stage in a TeamPCP chain that went by a number of developer ecosystems over a number of days earlier than reaching PyPI.
Focusing on logic is executed constantly all through the marketing campaign. Secret-rich infrastructure instruments present quick entry to wallet-adjacent supplies.
Potential penalties of this episode
The bullish case hinges on the velocity of detection and the dearth of publicly confirmed cryptocurrency thefts thus far.
PyPI remoted each variations by roughly 11:25 UTC on March twenty fourth. LiteLLM eliminated malicious builds, rotated maintainer credentials, and labored with Mandiant. PyPI is presently displaying 1.82.6 as the newest seen launch.
If defenders rotate secrets and techniques, audit litellm_init.pth, and deal with uncovered hosts as burned earlier than attackers convert leaked artifacts into energetic exploitation, the injury is proscribed to credential disclosure.
The incident additionally accelerates the adoption of a apply that’s already turning into in style. PyPI’s Trusted Publishing changed long-lived guide API tokens with short-lived OIDC-backed IDs, which roughly 45,000 tasks had adopted by November 2025.
The LiteLLM case concerned the misuse of launch credentials, making it extraordinarily tough to dismiss a change case.
For the crypto crew, this incident created an urgency to strengthen separation of roles. This implies chilly validator drawers are saved utterly offline, deployment signers are remoted, cloud credentials are short-lived, and the dependency graph is locked.
The DSPy crew’s fast repair and LiteLLM’s personal post-incident steering each level to sealed builds because the remediation normal.
Within the case of bears, there might be lag. SafeDep has documented payloads that leak secrets and techniques, unfold inside Kubernetes clusters, and set up persistence earlier than detection.
Operators who put in tainted dependencies inside their construct runners or cluster-connected environments on March twenty fourth might not uncover the complete extent of the hazard for a number of weeks. Extracted API keys, deployment credentials, and pockets information don’t expire upon discovery. The enemy can preserve them and act on them later.
Sonatype lists malicious availability as “at the least 2 hours.” LiteLLM’s personal steering is for installations as much as 16:00 UTC. FutureSearch’s quarantine timestamp is 11:25 UTC.
Groups can not rely solely on timestamp filtering to find out danger, as these numbers don’t present a very clear-cut outcome.
Essentially the most harmful eventualities on this class are centered round operators’ shared environments. If a crypto trade, validator operator, bridge crew, or RPC supplier installs a tainted transitive dependency inside a construct runner, your entire management aircraft will be uncovered.
Cross-namespace Kubernetes secret dump and privileged pod creation within the kube-system namespace are management aircraft entry instruments designed for lateral motion.
If that lateral motion reaches an setting the place sizzling or semi-hot validator materials is current on reachable machines, the consequences can vary from theft of private credentials to compromising validator privileges.
As a consequence of PyPI’s quarantine and LiteLLM’s incident response, the energetic distribution interval has ended.
Groups that put in or upgraded LiteLLM on March twenty fourth, or ran builds with unpinned transitive dependencies that resolve to 1.82.7 or 1.82.8, ought to deal with their environments as totally compromised.
Some actions embrace rotating all secrets and techniques accessible from uncovered machines, auditing litellm_init.pth, revoking and reissuing cloud credentials, and guaranteeing that no verification privilege materials is accessible from these hosts.
The LiteLLM incident paperwork the trail of an attacker who knew precisely what off-chain information to search for, had a supply mechanism with tens of tens of millions of month-to-month downloads, and constructed persistence earlier than anybody pulled the construct from distribution.
Off-chain mechanisms to maneuver and safe cryptocurrencies have been positioned straight within the payload’s search path.

Leave a Reply