On April 24, Mission Eleven awarded the Q-Day Prize to researcher Giancarlo Lelli, who used publicly accessible quantum {hardware} to derive a 15-bit elliptic curve personal key from a public key.
That is the most important public demonstration but of a category of assaults that would someday threaten Bitcoin, Ethereum, and all different programs secured by elliptic curve cryptography. The prize was 1 Bitcoin.
The irony is {that a} researcher obtained Bitcoin by breaking a miniature model of the arithmetic that protects it.
a A 15-bit key just isn’t as safe as Bitcoin’s 256-bit elliptic curve.and presently there is no such thing as a publicly identified quantum laptop that may break an actual Bitcoin pockets.
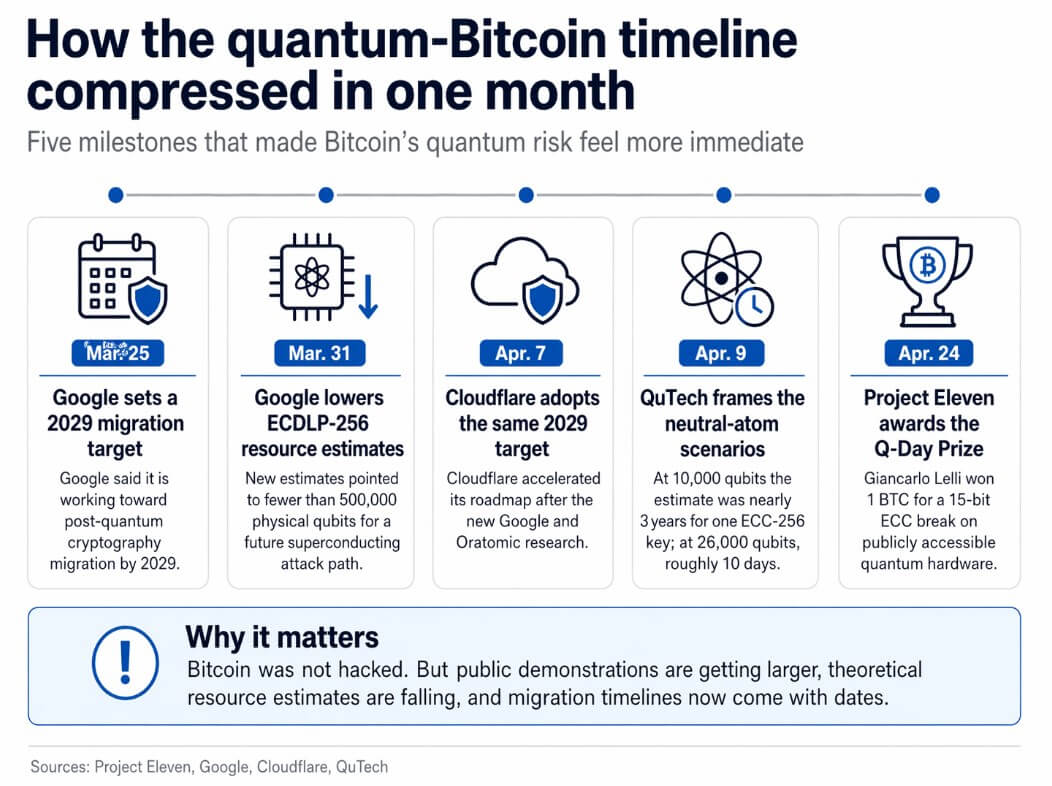
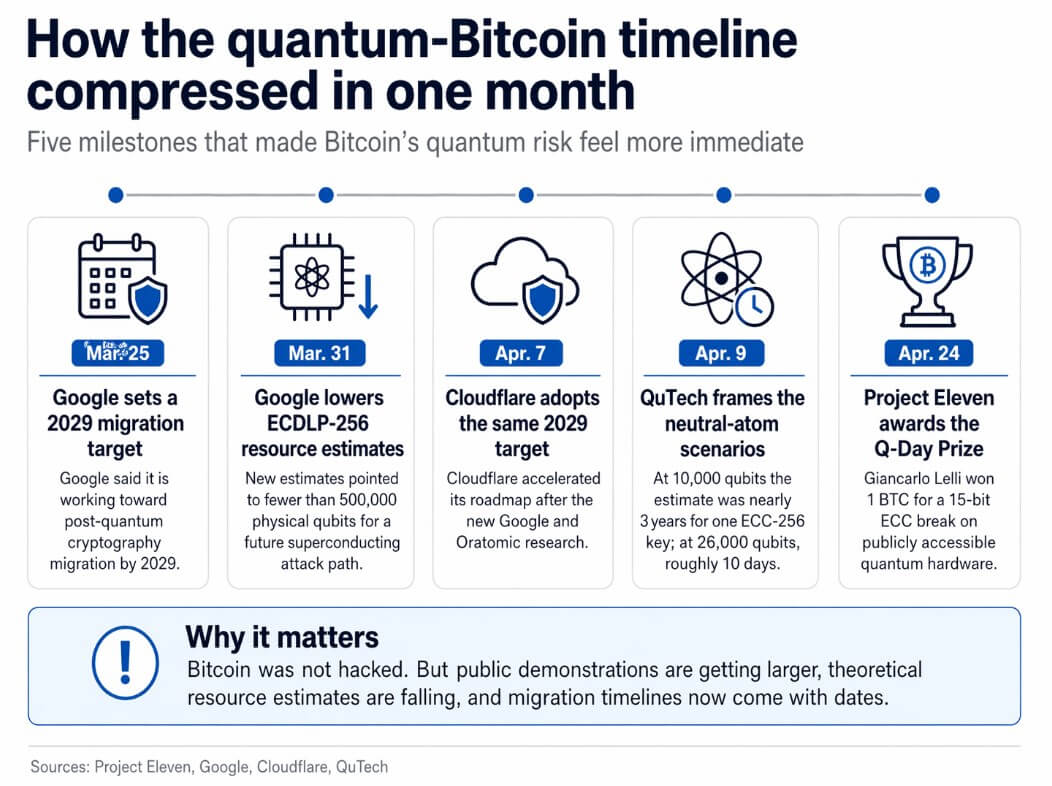
This consequence comes at a time when issues are getting fairly severe, with Google lowering its ECDLP-256 useful resource estimates and setting a 2029 migration deadline in the identical month.
What Leli truly did
Lelli used a variant of Scholl’s algorithm, a quantum algorithm focused on the elliptic curve discrete logarithm drawback, the mathematical foundation of Bitcoin’s signature scheme, to get well personal keys from public keys throughout a search house of 32,767.
The Q-Day prize competitors challenged members to crack the most important ECC key attainable on a quantum laptop with out utilizing any classical shortcuts or hybrid tips.
Lelli’s 15-bit consequence was one of the best amongst members to achieve the deadline, and Mission Eleven says it beats Steve Tippeconnic’s September 2025 6-bit demo by an element of 512.
In accordance with Mission Eleven, Decrypt studies that the successful machine has roughly 70 qubits, and that an unbiased committee that included researchers from the College of Wisconsin-Madison and qBraid reviewed the submissions.
The suitable body for this result’s a toy lock that was opened utilizing the identical set of strategies that may someday threaten the protected. The locksmith has been improved and the protected is in storage for now.
| Declare | What the article helps | why is it vital |
|---|---|---|
| Quantum laptop breaks 15-bit ECC key | Mission Eleven says Giancarlo Relli derived a 15-bit elliptic curve personal key from a public key utilizing publicly accessible quantum {hardware}. | Turning quantum threats into concrete public demonstrations relatively than purely theoretical warnings |
| Bitcoin itself has not been hacked | The article clearly states that presently, no publicly identified quantum laptop can crack an actual Bitcoin pockets. | This preserves the authenticity of the work and avoids exaggerating the outcomes |
| In consequence, the identical assault household associated to Bitcoin was used. | Lelli used a variant of Scholl’s algorithm for the elliptic curve discrete logarithm drawback, which is the premise of Bitcoin’s signature scheme. | Join toy demos to actual crypto dangers with out claiming equivalence |
| The demonstration passed off underneath restrictive guidelines | The Q-Day prize required entrants to crack the most important ECC key attainable on a quantum laptop with out utilizing classical shortcuts or hybrid tips. | Reinforces the significance of the outcomes as quantum benchmarks |
| Outcomes are higher than earlier public ECC demonstrations | Mission Eleven described the 15-bit outcomes as a 512x bounce over Steve Tippeconnic’s September 2025 6-bit demo. | Exhibits progress on the general public demonstration entrance |
| The hole with Bitcoin’s 256-bit safety stays giant | The article states that 15-bit keys are nowhere close to Bitcoin’s 256-bit elliptic curve safety. | That is the central warning the reader must accurately interpret the story |
| The {hardware} was nonetheless small by precise assault requirements. | The successful machine reportedly had round 70 qubits. | The achievement emphasizes its significance as a milestone relatively than proof {that a} full-scale assault is imminent. |
| The actual story is directional, not catastrophic | Public demos have gotten greater, useful resource estimates have been lowered, and migration deadlines have been set with concrete dates. | Threats stay in future tense, however timelines have gotten more and more tough to disregard |
The rationale this demo is extra vital than it was six months in the past is due to Google.
On March 31, Google introduced new ECDLP-256 useful resource estimates for circuits utilizing lower than 1,200 logical qubits and 90 million Toffoli gates, or lower than 1,450 logical qubits and 70 million Toffoli gates.
Google estimated that these circuits may run on quantum computer systems related to superconducting cryptography with fewer than 500,000 bodily qubits, about 20 occasions decrease than earlier estimates.
On March 25, Google set its personal post-quantum cryptography transition purpose for 2029, explicitly tying that deadline to advances in {hardware}, error correction, and useful resource estimation.
Cloudflare hit its 2029 purpose on April 7, citing each the Google paper and Caltech/Oratomic preprint as causes for the acceleration.
In that preprint, they claimed {that a} impartial atomic structure may run Scholl’s algorithm at cryptographically related scales utilizing simply 10,000 reconfigurable atomic qubits.
QuTech famous in an April 9 remark that at 10,000 qubits, this structure would nonetheless take almost three years to crack a single ECC-256 key, whereas a extra time-efficient 26,000 qubit configuration would carry execution time to about 10 days.
Each estimates depend on machines that do not but exist, and the Caltech/Oratomic research is an unreviewed preprint.
The helpful takeaway from these numbers is that for some theoretical architectures, the long-term {hardware} necessities are a lot decrease than what researchers envisioned a 12 months in the past.
Public demonstrations have turn into shorter, useful resource estimates have been lowered, and migration schedules now embody particular dates.
Bitcoin pockets is already public
Mission Eleven’s reside tracker presently lists 6,934,064 BTC as weak to quantum assaults.
This vulnerability implies that quantum assaults are most harmful when the general public secret’s already seen on the chain, which happens with previous deal with sorts, reused addresses, and partial spends.
Some Bitcoin wallets have already uncovered their public keys by earlier transactions. Google’s March 31 paper makes the image even clearer, declaring that crypto-related quantum computer systems with quick clocks may allow on-spend assaults on public reminiscence pool transactions, extending the danger from dormant previous wallets to precise spending.
Bitcoin governance is beginning to reply with BIP 360, which proposes a brand new output kind that eliminates Taproot’s quantum-vulnerable key cross spending. BIP 361 proposes a phase-out of legacy signatures that may drive the transition of quantum-vulnerable outputs.
Their existence confirms that Bitcoin has entered a transition section. The tougher query going ahead is whether or not decentralized networks can coordinate incentives, schedules, and dealing with of dormant and misplaced cash earlier than urgency outweighs coordination.
Two paths ahead
For bulls, migration turns into routine earlier than the emergency arrives.
Google and Cloudflare’s 2029 targets reset expectations throughout the trade, pockets suppliers and exchanges transfer customers away from long-exposure deal with patterns, and Bitcoin governance rallies round output modifications earlier than precise crypto-related quantum computer systems turn into a actuality.
Q-Day stays sooner or later tense, and essentially the most weak BTC inventory associated to public keys being uncovered will shrink because the {hardware} catches up.
Within the case of bears, assault vectors proceed to look extra like engineering than science fiction, outpacing governance responses.
Extra public key destruction demonstrations arrive, architecture-specific estimates drop once more, and the market begins to reprice weak UTXOs and long-idle cash.
The injury on this state of affairs begins with diminished belief, governance conflicts, and hasty transition planning across the clock. Decentralized networks with out a government that mandates deadlines face essentially the most tough model of that competitors.
| state of affairs | what’s going to change | What leaves you weak | Market/governance influence |
|---|---|---|---|
| bull case | Migration is routinely completed earlier than emergencies come up. Pockets suppliers, exchanges and protocol builders start to scale back public key publicity | Outdated deal with sorts, reused addresses, and a few dormant wallets nonetheless pose a danger till absolutely migrated | Belief is maintained as a result of the ecosystem treats quantum danger as an infrastructure improve relatively than a disaster |
| bear case | Public key destruction demonstrations proceed to enhance and {hardware}/useful resource estimates proceed to drop quicker than governance variations | Public keys, long-idle cash, partial spends, and reside spend transactions stay public for lengthy durations of time. | Markets start to reprice weak UTXOs, governance conflicts intensify, transitions happen underneath strain |
| The quickest strategy to scale back danger | Improved pockets well being, lowered deal with reuse, lowered public key publicity, new output sorts, and phasing out legacy signatures | Coordination points stay, particularly relating to misplaced cash and sluggish person motion. | The community buys time and reduces the variety of cash uncovered to the general public earlier than cryptographically associated quantum machines exist. |
| What’s most pressing? | Massive-scale public demonstrations, decrease {hardware} estimates, quicker clock architectures, and robust proof that on-spend or reminiscence pool assaults can turn into viable. | Wallets with public keys already seen can be extra delicate to future advances. | The dialogue shifts from “Ought to I put together?” “How briskly can Bitcoin modify?” |
| Vital exterior deadlines | Google and Cloudflare are concentrating on 2029. UK NCSC units milestones for 2028, 2031 and 2035 | Decentralized crypto networks can not transfer as shortly as centralized corporations by default | Bitcoin faces more durable migration competitors because it depends on decentralized coordination relatively than a single authority |
| remaining consequence | In one of the best case, Q-Day stays sooner or later tense lengthy sufficient for migration to remain forward of the menace. | Within the worst case state of affairs, technological advances outpace social and governance responses. | The actual danger lies not solely within the potential to finally break the lock, however in whether or not the ecosystem can modify earlier than urgency outweighs adjustment. |
The UK’s Nationwide Cyber Safety Heart has set transition milestones for 2028, 2031 and 2035. Google and Cloudflare are each concentrating on 2029.
The Ethereum Basis says a world decentralized protocol transition will take years and desires to begin earlier than threats arrive.
Bitcoin’s quantum menace presently exists in public demonstrations, company migration calendars, and draft protocol proposals.


Leave a Reply